Don’t let the discovery of a cyber breach be the first time you’ve thought about how you will handle it.
Overnight, your information security team discovered unauthorized access to sensitive files. Early this morning, your technology team confirmed some file IDs have been changed and cannot be accessed. Both teams propose taking the network offline until they can find the root cause. This means your people can’t work and your customers can’t use your services, potentially for days.
You don’t know how much information has been accessed, what has been done with it, who has it or for how long. You do know that you cannot serve your customers and, if their accounts have been compromised, their businesses could also be at risk.
This is now your job for the foreseeable future. Good morning.
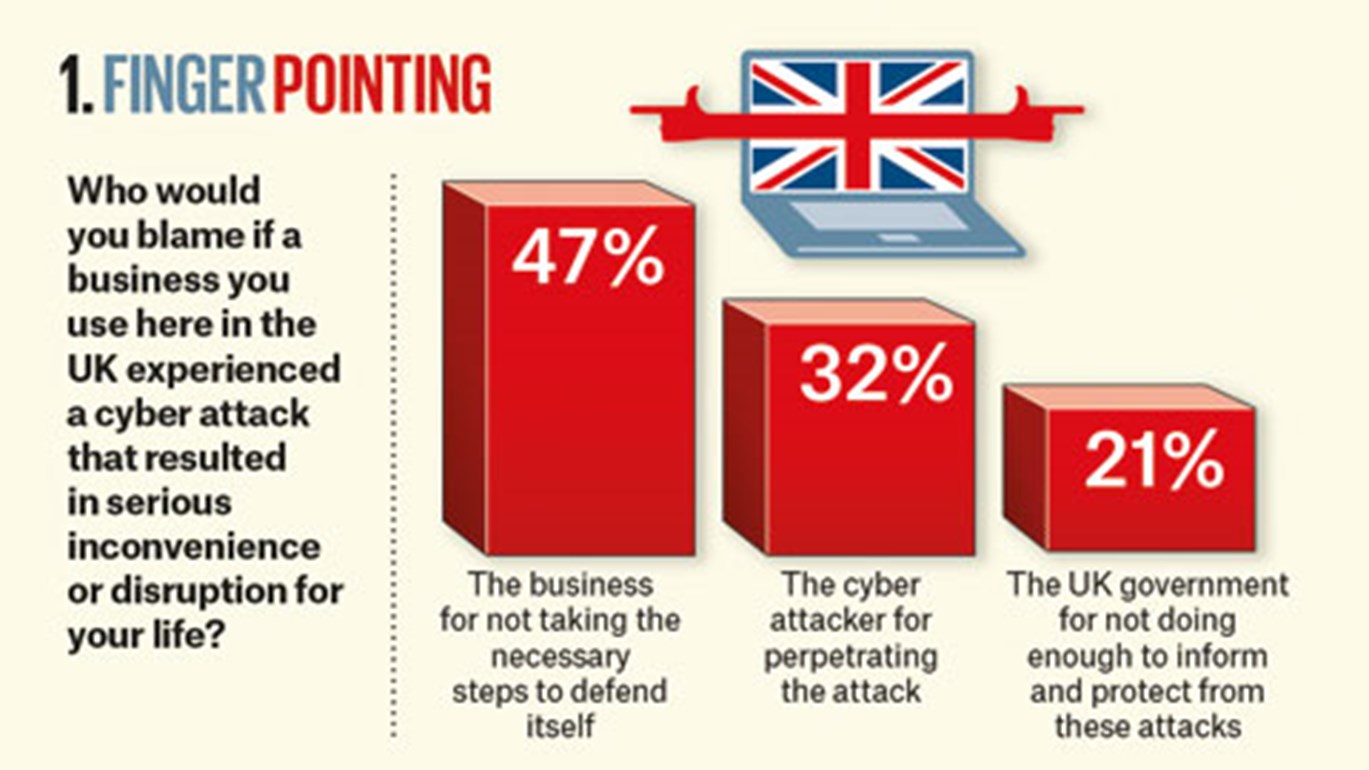
Blame Game
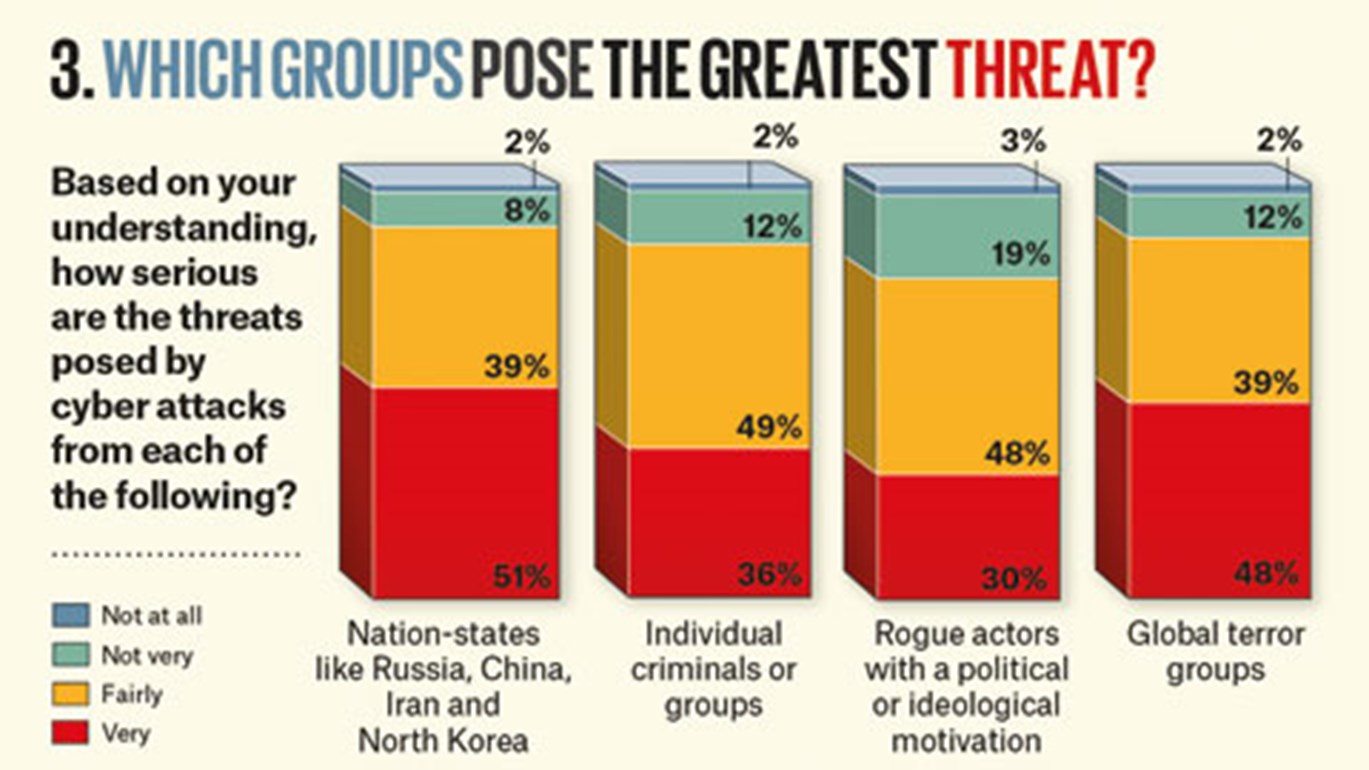
Your company is now in the spotlight. Rightly or wrongly, in the case of a cyber incident, the brunt of the blame falls on the victim of the attack – not the perpetrator. In a Brunswick Insight survey, financial media readers in the UK indicated that they’re well aware of the usual suspects who carry out these attacks. Nearly nine in 10 respondents recognize serious threats from nation-state actors, global terror groups and individual criminals. Even so, nearly half (47 percent) say they’d blame the business that fell victim to the attack, compared to just 32 percent who would blame the perpetrator (Chart 1 on next page).
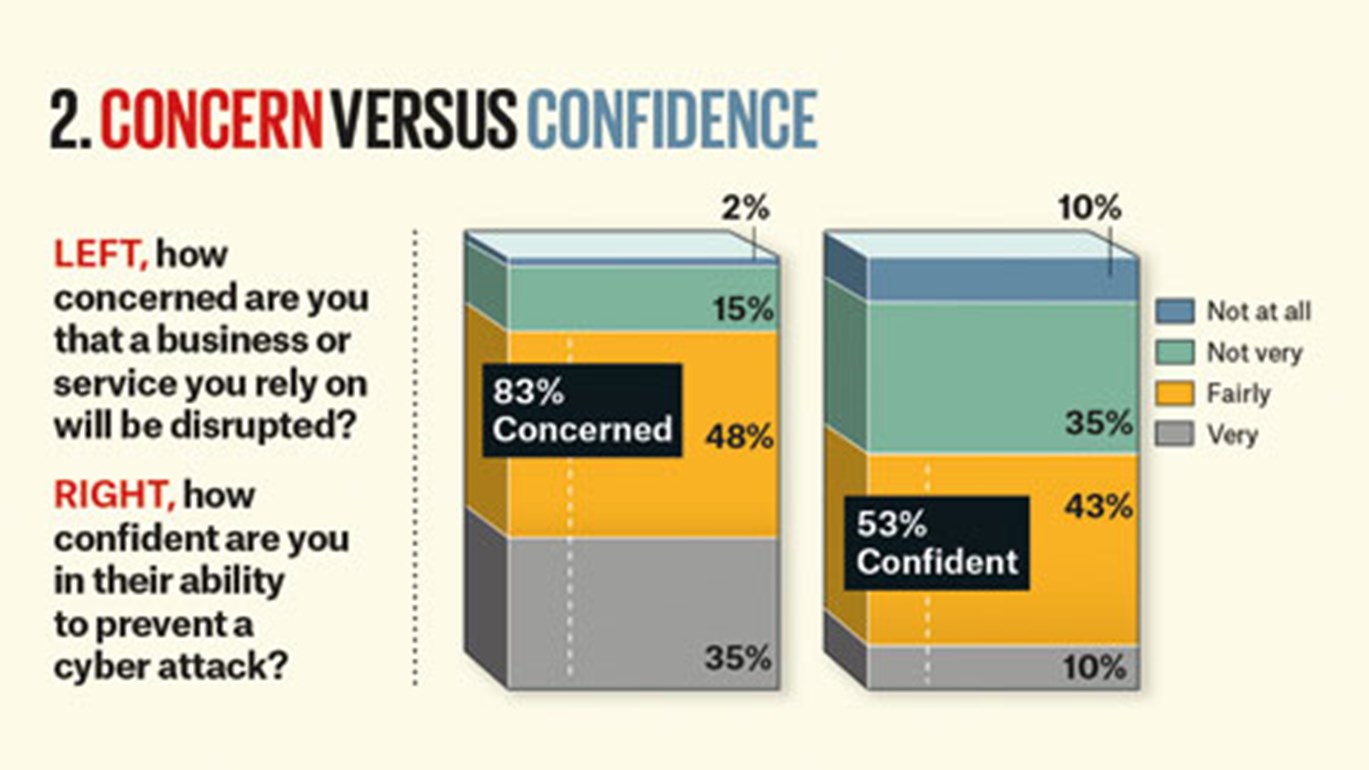
Companies not meeting expectations of preparedness are the biggest target for blame. In our survey, 83 percent say they’re concerned services they rely on will be disrupted (Chart 2); just 53 percent say they’re confident those businesses can prevent an attack. Only 10 percent say they’re very confident.
Cyber attack headlines are now part of our daily newsfeed. Perhaps we are more accepting of the idea that our personal data has been breached, and we know we bear some of the responsibility to watch out for fraud. But we still expect companies to take all the right steps, mainly because:
You should have seen this coming. “When, not if” has long been a stark warning from cyber experts and regulators.
You should have been better prepared. Despite growing awareness that business can be brought to a standstill, adequate steps are rarely taken in advance.
It Matters
These events have consequences for leadership, employees, customers, partners and investors. Each expects that the appropriate steps are being taken by the others to protect the company and sensitive information. But do they all understand the potential financial and reputational consequences?
Regulatory repercussions. The General Data Protection Regulation took effect in May of 2018. We don’t know yet what fines for the worst offenders will be, but they could amount to 4 percent of global turnover. The regulator could also force companies to suspend business if they aren’t satisfied the proper steps to protect data have been taken.
Loss of business. The June 2017 NotPetya attack aimed at the Ukraine caused material sales impacts for a number of global companies. They were simply collateral damage, the result of perhaps even just one user clicking on malicious links. Maersk has used the experience to warn others. They reported $265 million lost sales in a quarter following a 10-day period where the company was reduced to pen and paper while it reinstalled all of its IT systems.
Share price impact. Breached companies see immediate share price impact and underperform the market in the long term. An analysis by Comparitech of 28 breaches showed that these companies underperformed the Nasdaq by 4.6 percent over the first 14 days and by 11.35 percent over two years.
Lost productivity. Responding to cyber attacks weighs on your company’s performance. Production loss accounts for one-third of a company’s annualized costs due to cyber crime, the 2017 Accenture and Ponemon study found.
Executives are collateral damage. Companies that have suffered major breaches, like Yahoo!, Equifax, Target and Uber, often see the resignations of either their CEO, CISO and/or General Counsel.
Class action lawsuits. These are not limited to the US. We saw a firm threaten a group action suit against British Airways within days of the September 2018 data breach.